Patient Care (EHR) Solutions on Microsoft Surface
Discover the features that make Surface devices ideal for modern healthcare settings. This brochure shows everything from easy management and built-in security to flexible power and data options.
View: Patient Care (EHR) Solutions on Microsoft Surface
Medivis Case Study
At Providence Swedish, neurosurgeons are leveraging the Microsoft Surface HoloLens 2 to visualize complex neurosurgical procedures prior to the operation. Check out this case study to learn more about how Providence is leveraging this technology—and for inspiration to help you innovate with the HoloLens 2.
Cyber resilience programs falling short on preparing workers for a crisis
The report from Immersive Labs raises questions about whether corporate employees would know how to respond after a major cyberattack.
Drive your on-premises workloads to the checkered flag, fueled by vSphere+
Like many organizations, your enterprise may choose to run some or all of its workloads in an on-premises data center. With VMware vSphere,+ you can bring the benefits of cloud infrastructure services to your on-prem workloads. View this infographic to see how.
View: Drive your on-premises workloads to the checkered flag, fueled by vSphere+
The Guide to Key Management as a Service (KMaaS)
Security leaders recognize that one of the most effective ways to ensure data security is through encryption and proper key management.
And the best way to facilitate this critical task is with a Key Management as a Service (KMaaS) solution that allows companies to manage encryption keys through a cloud-based solution instead of running the service on physical, on-premises hardware.
Read the blog to understand how KMaaS works and why it's a game changer in security operations. Get in touch with one of our experts to request a demo.
Introducing Microsoft Security Copilot: Empowering defenders at the speed of AI
Discover the future of cybersecurity with Microsoft Security Copilot, a groundbreaking security solution that empowers defenders to combat advanced threats at the speed and scale of AI. In Microsoft blog post, learn how Security Copilot empowers defenders with real-time threat intelligence, proactive response capabilities and seamless integration into security infrastructure. Gain valuable insights into the next cybersecurity frontier. Read "Introducing Microsoft Security Copilot: Empowering defenders at the speed of AI," right here.
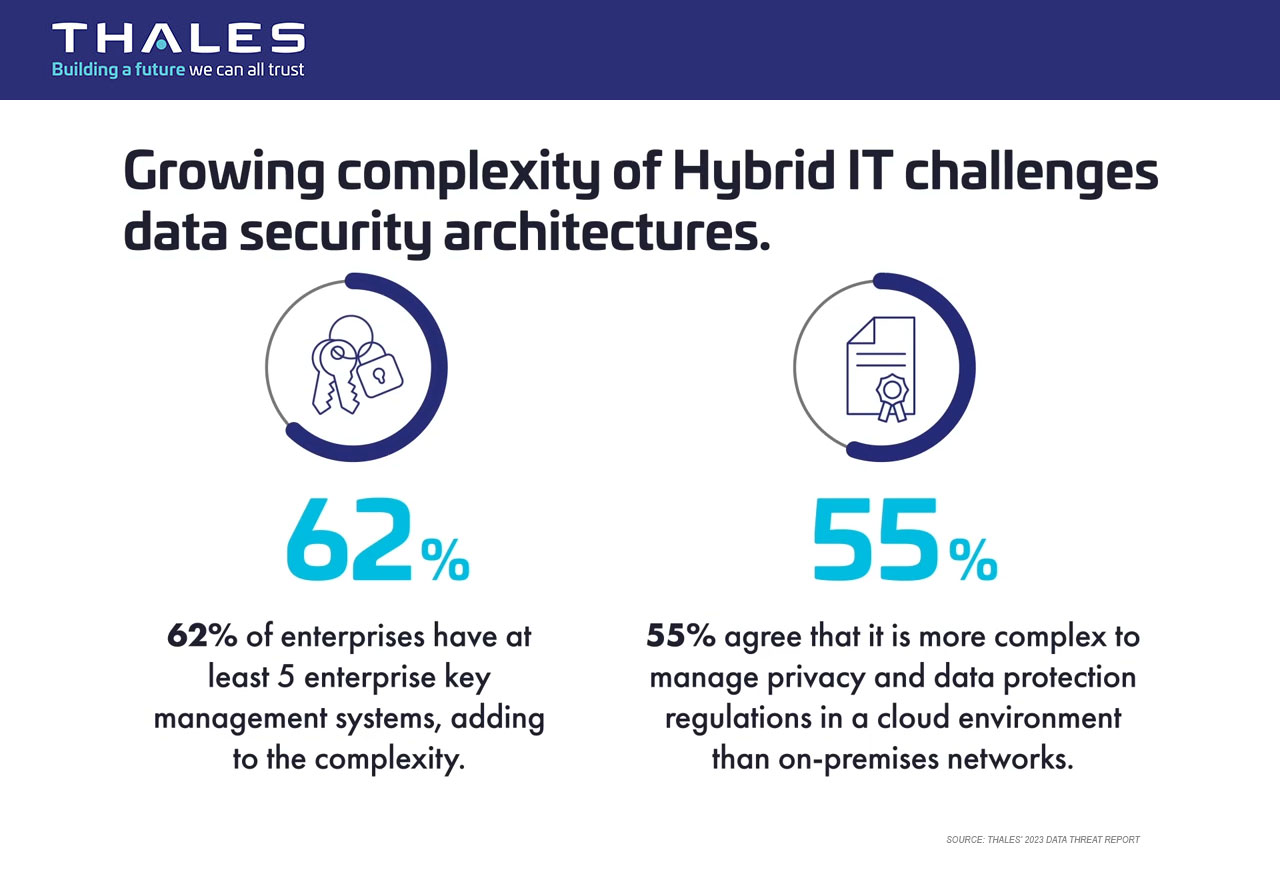
Thales Announces CipherTrust Data Security Platform as-a-Service
Continuing its long tradition of cybersecurity innovation, Thales just unveiled the CipherTrust Data Security Platform as-a-Service, a groundbreaking solution that allows businesses to rapidly deploy and scale key management and data security services without the need to manage hardware and to centrally maintain and control their encryption keys securely across cloud environments. Read the press release for details and contact a certified Thales partner at Divergent IT to discuss flexible pricing and implementation options.
Is cybersecurity an unsolvable problem?
Ars chats with law philosopher Scott Shapiro about his new book, Fancy Bear Goes Phishing.
Why Load Balancers Should be Part of Your Security Architecture
Larry Goldman of Progress points out why your security architecture needs load balancers.