eSentire Endpoint Services
In the Solution Brief titled *eSentire Endpoint Services*, readers will learn about comprehensive protection strategies against modern cyber threats. The brief describes eSentire's Managed Detection and Response (MDR) service, which provides advanced endpoint protection, leveraging 24/7 threat hunting, investigation, and threat response. Key points include the interdiction of ransomware, zero-day attacks, and advanced persistent threats (APTs), alongside behaviors such as abnormal activity and lateral movement. Additionally, the brief highlights the cost-effective endpoint protection offered via the eSentire Agent, which employs deep learning technology. Moreover, it showcases eSentire's collaboration with industry-leading partners like CrowdStrike and Microsoft, offering bring your own license options which can enhance the reseller's service offerings. The brief also emphasizes eSentire's use of its unique BlueSteel machine learning engine to increase PowerShell threat detection accuracy, staying ahead of attackers by leveraging advanced analytics. This is essential reading for businesses looking to advance their cybersecurity posture and minimize business disruptions due to cyber attacks. Learn how our reseller can assist you in integrating eSentire's solutions into your security strategy.
View: eSentire Endpoint Services
Implementing Zero Trust Best Practices
Discover the benefits of Aruba Edge-to-Cloud Security with Zero Trust. This solution brief has the details and the best practices you need to know for implementation.
View: Implementing Zero Trust Best Practices
The Private Cloud Revolution: How Artificial Intelligence Is Transforming IT Infrastructure
The world of technology is rapidly evolving, and one of the most significant changes is the combination of artificial intelligence (AI) and private cloud systems. This isn't just an update. It fundamentally changes IT operations, dramatically improving efficiency, scalability, and security.
is here when you're ready to get serious about implementing AI in your organization.
Modern Devices for Nonprofits
This solution brief on Surface for nonprofits highlights the new AI experiences available with Surface with Windows 11 and Copilot as well as the productive, safe workplace available with deploying Microsoft 365.
View: Modern Devices for Nonprofits
The First 90 Days: How to Prepare for Your First Board Meeting as a Security Leader
Starting as a new security leader means making a strong impact in your first three months. The eBook from eSentire helps you establish credibility with senior management and align cyber risk strategies with business goals. Focused on measurable outcomes and a clear understanding of your company's cyber risk, this guide enables you to reshape your security framework for business success. Use the insights for both initial interactions and long-term planning.
As your tech reseller partner, we're ready to connect you with an eSentire solution that support these key initiatives.
View: The First 90 Days: How to Prepare for Your First Board Meeting as a Security Leader
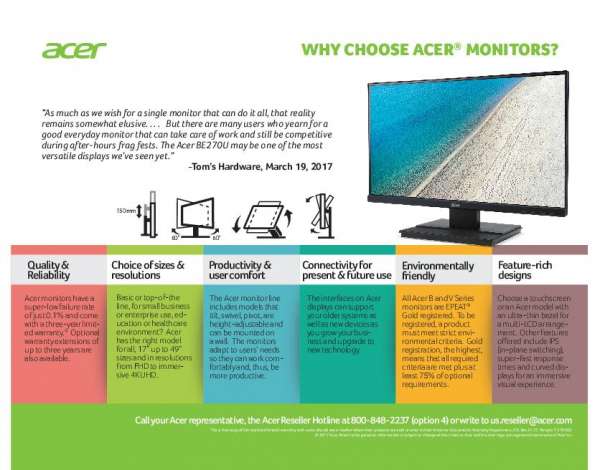
Why Choose Acer Monitors?
Because a superior viewing experience is a critical element of a productive and happy hybrid workforce, Acer offers a world-class portfolio of monitors, with models ranging from 17" to 49" and in resolutions from FHD to immersive 4K UHD.
Acer's planet-friendly, super-reliable monitors offer a ton of great features and benefits your hybrid workforce will love.
Ready to discuss flexible pricing options? Divergent IT can set you up with the Acer monitors that best fit your needs.
View: Why Choose Acer Monitors?
Zero trust security is your best defense 🔐against threats to data and applications. Reply to learn how Divergent IT can offer complete endpoint protection with @Dell solutions.
The 2024 Work Trend Index: AI at Work Is Here. Now Comes the Hard Part
AI is already embedded in a wide range of applications, and many employees use AI tools on their own to help them in their work. This survey report, the 2024 Work Trend Index by Microsoft and LinkedIn, found that 3 in every 4 knowledge workers use AI tools, and 79% of leaders agree their company needs to adopt AI to stay competitive. Read this report to see the results of this extensive survey and find out what steps your enterprise can take to prepare for full AI adoption into your workplace.
eSentire MDR Foundations
Rethink your cyber defense with eSentire MDR Foundations. MDR Foundations combines the advanced protection of MDR for Endpoint with eSentire's MDR for Log, enabling 24/7 multi-signal ingestion and complete threat visibility across your endpoints, applications, and cloud services. It leverages existing EDR/EPP solutions, reducing operation costs, and ensuring compliance with regulatory standards.
Optimize security investments with actionable intelligence and resilient endpoint protection. Contact us for insights on implementation.
View: eSentire MDR Foundations