eSentire Endpoint Services
In the Solution Brief titled *eSentire Endpoint Services*, readers will learn about comprehensive protection strategies against modern…
Implementing Zero Trust Best Practices
Discover the benefits of Aruba Edge-to-Cloud Security with Zero Trust. This solution brief has the details and the best practices you need…
The Private Cloud Revolution: How Artificial Intelligence Is Transforming IT Infrastructure
The world of technology is rapidly evolving, and one of the most significant changes is the combination of artificial intelligence (AI) and…
Modern Devices for Nonprofits
This solution brief on Surface for nonprofits highlights the new AI experiences available with Surface with Windows 11 and Copilot as well…
The First 90 Days: How to Prepare for Your First Board Meeting as a Security Leader
Starting as a new security leader means making a strong impact in your first three months. The eBook from eSentire helps you establish…
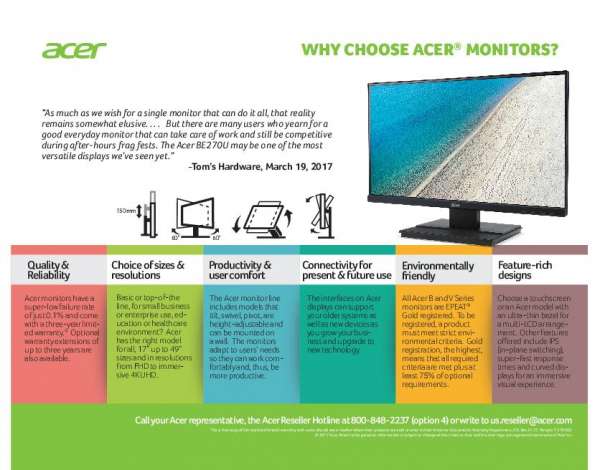
Why Choose Acer Monitors?
Because a superior viewing experience is a critical element of a productive and happy hybrid workforce, Acer offers a world-class portfolio…
Zero trust security is your best defense 🔐against threats to data and applications. Reply to learn how Divergent IT can offer complete endpoint protection with @Dell solutions.
Zero trust security is your best defense 🔐against…
The 2024 Work Trend Index: AI at Work Is Here. Now Comes the Hard Part
AI is already embedded in a wide range of applications, and many employees use AI tools on their own to help them in their work. This…
eSentire MDR Foundations
Rethink your cyber defense with eSentire MDR Foundations. MDR Foundations combines the advanced protection of MDR for Endpoint with…